 Business
Business
- +91-120-4234350
- +1-925-272-0857
- +46-709-96-86-22
- +65 9359 9621
 Case Study
Case Study
Client Profile
Our client is a global equity financial company based in Sweden. Information related to the current stocks
on the loose is provided to its customers to help get the better of most of the deals.
Business Challenge
A growing share of people now use smartphones as their primary means of online access at home. Hence
the client decided to catch on to the times of smartphone and launch a business app (Android/iOS) based
on the already existing website. Since the dilemma of the sensitivity of the data on both the mobile app
and the website they felt suspicious of the hackers and required a comprehensive solution to manage and
secure the data transactions by servers to the mobile app.
The client was looking to provide the consumers with absolute data (statistics) that can be highly relied
upon.
Suretek Solution
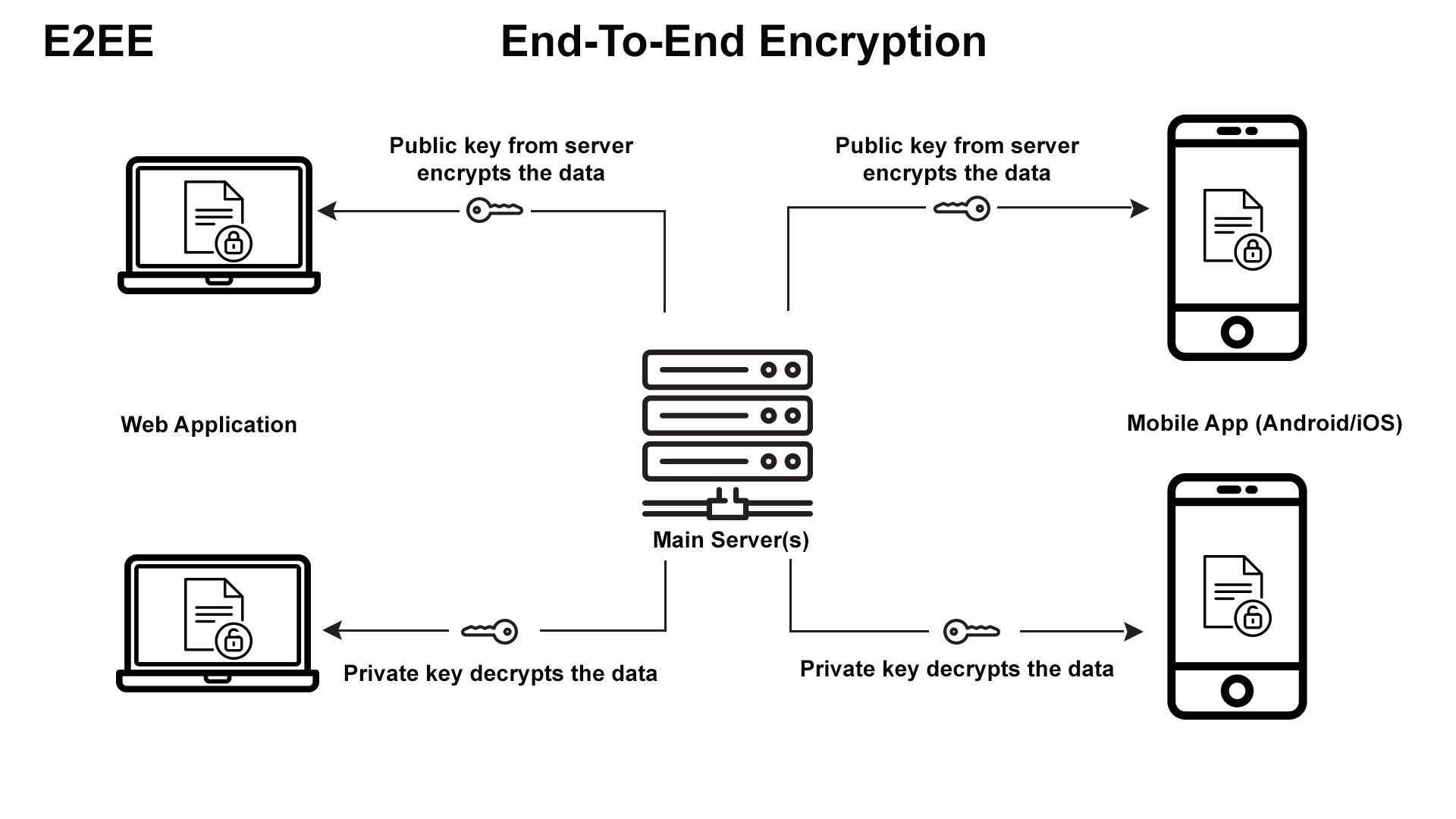
Suretek alongside its client calculated the business requirements and developed a technical solution to
realize the business vision. Suretek proposed the use of End-to-End encryption over the network to secure
the data revolving around investment in stocks per se.
Tailored to the client’s specific needs we built encryption into their proposed platforms with cost saving
methodologies. The solution included intrusion detection along with the fact that end-to-end encryption
was implemented to the client’s solution.
Suretek's Contribution And Work Profile Following aspects have been given priority when developing the web application.
 Technologies Used
Signal Protocol, CryptoSwitch, Py(NaCL)
Technologies Used
Signal Protocol, CryptoSwitch, Py(NaCL)
We welcome you to contact us and know more about how we can add value to your business.

Suretek Infosoft is a young expanding offshore IT/Software technology services Company that provides intelligent, reliable and cost effective solutions at highest quality levels.
Suretek Infosoft Pvt Ltd
D-247/32,
Sector 63, Noida
Uttar Pradesh - 201301
NCR (Near New Delhi)
Email Us: info@suretekinfosoft.com
Contact Us: +91-120-4234350